As a first-time researcher, one may face diverse challenges when trying to gather everything needed to complete a given project. According to the textbook, it does not matter the level of a student since most researches often provoke anxieties. However, one thing that one must be aware of is that a person’s decision to proceed with a given research project is dependent on a variety of factors. For instance, a student must begin by gathering statistics about the chosen topic, analyzing existing policies that have been drafted in helping solve the problem, and conducting interviews to ascertain the prevalence of the identified problem (Blaxter et al., n.p). Engaging in the mentioned activities is crucial since it will provide more insights on how well a given topic should be handled. According to the textbook, research can be conveyed from different viewpoints. The first viewpoint notes that research can be presented in a fixed, linear series of stages. Occasionally, the linear series often has a distinct start and end. On the other hand, research can also be portrayed as a circular process whereby the last stages can be used in reinterpreting the steps that had been followed earlier (Blaxter et al., n.p). Despite having an idea of how research should be presented, having the required skills, resources and knowledge will lay a foundation for completing a given research.
1.1: Skills, Resources, and Knowledge that I already have
Although there are numerous skills, resources, and knowledge needed in completing a given research, I believe I uphold some of them, and they will serve as a guide in enabling me to complete this research. Having the necessary skills and resources is crucial since it lays a foundation for one to constantly improve themselves in areas that are not perfect. One of the essential research skills that I have relates to goal setting. Goal setting is vital in research since it gives one an idea of the final outcome of research. Goal setting is not only limited to one thing since it involves various aspects such as proper time management, planning, and organization. Being organized is vital in research since it helps one stick to the intended purpose of research, preventing one from making mistakes. The other essential skills that I possess relate to data collection. My data collection skills go beyond observing and conducting interviews. Being able to gather a wide range of facts and information from the internet has often helped me fulfill my data collection needs. The last important skill that I possess relates to proper report writing. When instructed to write, I can effectively use the required format, include a summary if needed, proofreading and sticking to the initial goal.
Having the relevant resources in research is equally a crucial element. Some of the resources that I already have include capital and support networks from different people. Effectively managing my capital will help me ensure that no aspect of the research is not fulfilled. Support networks will help me go a long way in completing this project since they will give me crucial information, especially during interviews.
Lastly, having sufficient knowledge will also help me include the necessary information related to the subject matter. Since I know how to gather information from the internet, I will use this knowledge in finding the relevant information from the internet, searching for the pertinent questions related to the topic, and exploring deeper options for solving a given subject matter.
1.2: Expanding on Past Successes
Some of the identified skills, resources, and knowledge can adequately cater to my current needs. Some of the areas that can sufficiently cater for my needs include goal setting and data collection skills. Having these skills will help me go a long way in prioritizing what to fulfill in my research. However, I need to develop my time management skills in the future. This is attributed to the fact that sometimes, it is challenging to accomplish all my goals within a set time frame. Although I have vast knowledge about the research topic that I will be analyzing, the changing technologies make it challenging to get all the necessary resources. As a result, I believe that gathering adequate knowledge in matters of using the current technologies will help fulfill all my needs in the future.
2.3: Key Questions That My Research Seeks to Address
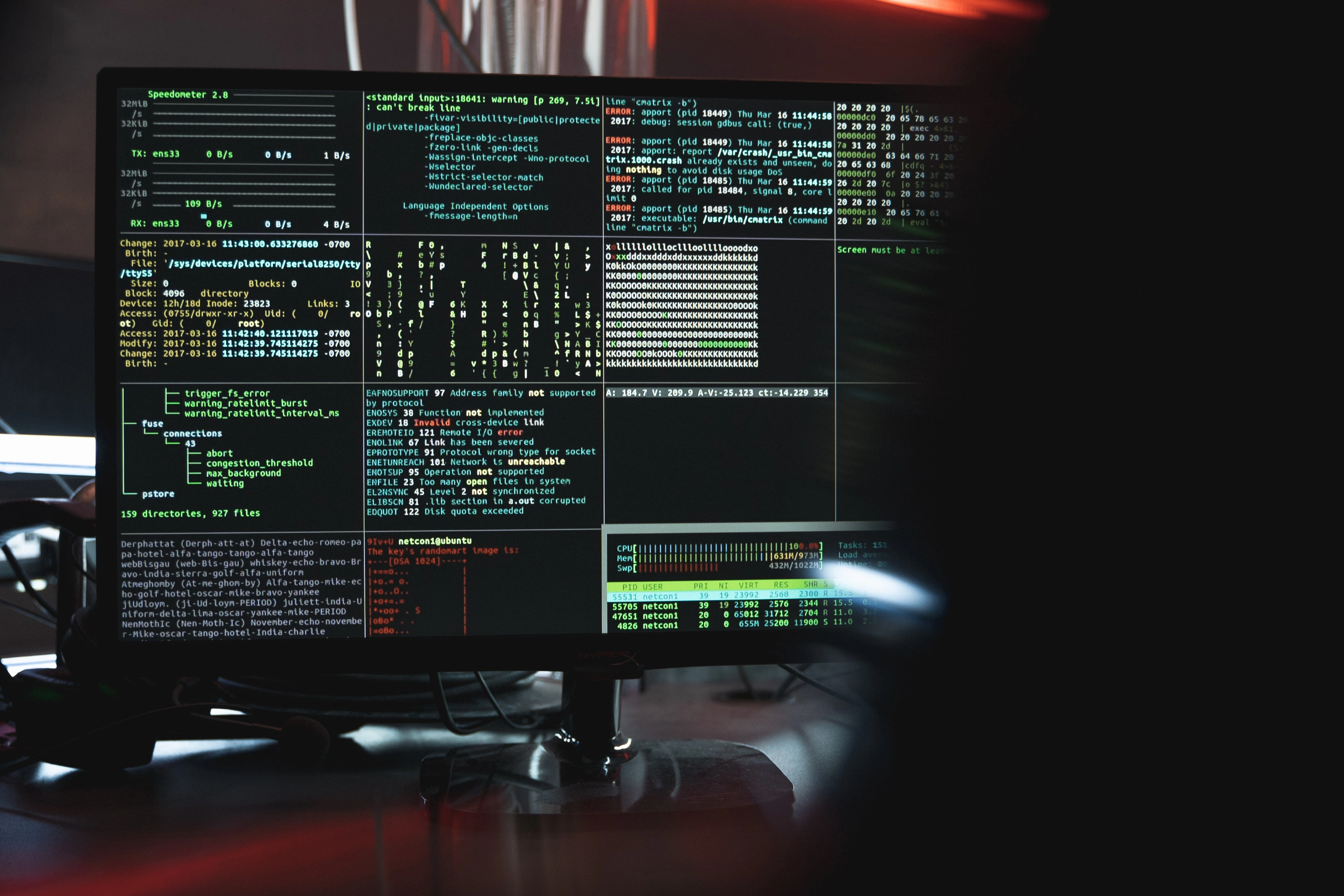
Cybersecurity and hacking are some of the common security concerns that have emerged with the current trends technological trends. Cybersecurity refers to the process of protecting computer systems and networks from disclosing information to third parties, theft, or damage. With the continued reliance on computer systems, the internet, and wireless networks, most organizations are instituting measures to protect vulnerable information.
On the other hand, hacking relates to the process of identifying any weakness in a computer system or network. After identifying the security weakness, a hacker often gains access to personal data or business data, which they can sell in the black market or use to blackmail an organization. One example of computer hacking relates to cracking passwords to gain access to a computer system. In the modern corporate world, most organizations depend on computers to successfully run their activities. As a result, most computers need to be constantly networked since this allows easy communication with external businesses. It is the networking of these computers that predisposes them to the outside world and hacking. Different types of hackers are often classified based on the intention of their actions.
This research topic is interesting to me since with the emergence of new technologies, security hackers are also devising methods of sophisticated techniques that can help them successfully gain access to classified information in different organizations without getting official authorization. By analyzing this topic in my research, I will expound on some of the common security aspects that predispose organizations to cybersecurity threats, especially from hackers. Additionally, expounding further into these research methods will lay a foundation for identifying effective strategies that can assist an organization in addressing its cybersecurity threats effectively. The following research questions will be used as a guide in successfully completing this research.
Research Question One
What are the current cyber security and data protection laws?
Research question Two
How can networks successfully prevent network attacks from hackers?
Research Question Three
What is vulnerability scanning, and what are some of the advantages associated with vulnerability scanning in preventing cyber security attacks?
Research Question Four
How can cyber-attack such as hacking cripple a company’s operations?
Reasons Why I Find Each Topic Interesting and Subfields in Each Topic That Relates to Security Systems
Cybersecurity and hacking are interesting to me because, with the emerging technologies, it provides room for generating various strategies that can be used to enhance the security of different computers.
Literature Review
Subfields related to each topic: Cybersecurity
Vulnerability and attacks: Vulnerability and attacks is one of the common aspects related to cybersecurity. A vulnerability denotes any weakness in a design or internal control. Most of the existing vulnerabilities can be reverse engineered or exploited using automated tools or scripts that have been customized to fulfill specific functions (Schatz et al., 8). A wide range of vulnerability attacks can serve as cybersecurity threats to a given computer system. One of the threats is classified as a backdoor. Backdoor is any secret method that can be used to bypass the normal authentication or security controls of any given computer (Schatz et al.,8). Most backdoor attacks can be either added by an authorized party or by an attacker with malicious reasons. The other attack relates to a denial of service attack (DOS). Most DOS attacks are geared towards hiding the availability of a given network resource to its intended users (Schatz et al., 8).
Vulnerability scanning: Vulnerability scanning is the process of assessing computers, networks, or applications for any known security weaknesses. When vulnerability scans are conducted appropriately, they can detect and classify the existing weaknesses on a computer, network, or any communication gadget. After conducting the vulnerability scans, effective countermeasures can be instituted to solve the existing vulnerabilities. Non-intrusive and intrusive vulnerability assessments are the two common forms of vulnerability scans. Using non-intrusive vulnerability scans, an organization can successfully identify vulnerabilities and create a report to solve them. Using the non-intrusive techniques is suitable since it does not create actual vulnerability exploitation during the scanning process. On the other hand, the intrusive assessment exploits vulnerabilities after the non-intrusive methods have discovered them.
Hacking Subfields
Types of Hackers
Different hackers often break into computer systems intending to fulfill various activities. According to ethical hackers, they often gain access to computer systems to fix some of the identified problems (Patil et al., n.p). Most ethical hackers also conduct penetration testing and vulnerability assessment on a wide range of computer networks. On the other hand, a cracker is a hacker who can breaks into a computer without proper authorization for personal gain (Patil et al., n.p). Most crackers intend to steal business data, violate privacy data, or transfer funds from a given bank account.
Effects of Hacking on a Company’s Operations
Computer hacking can lead to detrimental results in any given organization. For instance, when a cracker gains access to an organization’s data, they can steal sensitive information such as business documents, trade secrets, or contact information for employees. Additionally, by a hacker gaining access to a company’s information, they can erase or change data, leaving an organization with numerous losses. With the outlined aspects of my research, delving deeper into matters related to cyber security and hacking will lay a foundation for identifying recommendations that can help prevent cybersecurity threats and hacking.
Works Cited
Blaxter, Loraine, Christina Hughes, and Malcolm Tight. How to research. McGraw-Hill Education (UK), 2010.
Patil, Sonali, et al. “Ethical hacking: The need for cyber security.” 2017 IEEE International Conference on Power, Control, Signals and Instrumentation Engineering (ICPCSI). IEEE, 2017.
Schatz, D., Schatz, Daniel, Rabih Bashroush, and Julie Wall. “Towards a more representative definition of cyber security.” Journal of Digital Forensics, Security and Law 12.2 (2017): 8.